IP addresses for vanity - yes, the date can sometimes be important.
sysadmin - 10.1.2006 - 1.4.2006
WordPattern - probably the next one for today?
IBM offers bounty for Exchange customers - clear message (although Notes vs. Exchange is like "driving out the devil with Beelzebub" to me)
TUD:OS - TU Dresden Operating Systems - a few determined individuals keep the idea of the microkernel alive. Good so!
Shit hits Fan with Debian?
When Joey throws in the towel - and does so publicly - then the story must really be hitting the fan. Because normally he just quietly fades away ...
Mac OS X Security Challenge
The Mac OS X Security Challenge by the University of Wisconsin is a much more realistic variant of the rather dubious "30-minute hack" that is currently haunting the press and blogs. Because on the box hacked in 30 minutes, the attackers had a user account - it was therefore a simple privilege escalation, not a remote hack. The latter is quite different to set up, as you first have to get access to the machine.
Nevertheless, Apple should of course also take privilege escalations seriously - because, for example, on publicly accessible computers there are already some attack scenarios that are quite problematic - especially with alleged security features. For example, the encrypted home directory becomes a farce if multiple users can be logged in at the same time on the computer - the home directory is opened and mounted when the first user logs in, the second user can then simply look in. Apple should already improve at such points, of course also at the points where an unprivileged user can get root rights - because these are attack vectors for viruses and Trojans.
Hey, I don't feel like having similar nonsense like under Windows in the long run, so make sure you close the holes at Apple!
Net Neutrality and Reality
Good points from Doc Searls in "[Net Neutrality vs. Net Neutering[0]":
The carriers' plan from the beginning has been to convert the Net into a paid content delivery system--of some kind. That's all they were ever able to imagine. That's why they've screwed Net Neutrality from the beginning, offering crippled asymmetrical service to customers whom they expected only would consume, never producing much more than clicks that brought down more to consume. Most of us have never known anything but an asymmetrical relationship with the Net, which is why so many of us barely can imagine what it means to be a producer as well as a consumer in the Net's end-to-end world. A couple of days ago, a woman I know--middle class, white collar--told me she doesn't like the Net because "I don't like mass media in general".
ADSL, modems with limited upstream, dynamic IPs for dial-up users without even attempting to reassign the same IP, forced disconnects with IP changes on DSL flat rates - net neutrality does not exist for many users. Sure, you can get a free blog somewhere - but you always remain a second-class network user. The simplest thing - running your own site on your home computer - is hardly available to any network user.
The flip side of the coin: would we (we = sysadmins) want all those people at home to run servers who are not even able to protect their Windows rudimentarily against attacks? What would a network look like in which every user is also a producer and runs the necessary software - would the attacks and break-ins be enough incentive for manufacturers to make the software user-friendly so that the security level would be higher, or would the chaos be even greater, with a few million more zombie computers?
Is it an alternative to encourage people to rent root servers or to pool with friends and rent one together - knowing full well that most of them have no idea about administration and, given the current state of server software, are more likely to catch additional holes than plug them and thus unwittingly participate in spam distribution, DOS and other network nasties? Would server hosts take better care of and secure the systems if they rented more of them to clueless users?
Or would this just be another September that never ends?
SharedAppVNC - interesting VNC variant that only replicates application windows, not the entire desktop. Also with special OS X support.
Larry's Distorted Reality
I sometimes really wonder what kind of herb Larry Ellison smokes to come up with such nonsense:
"Open source becomes successful when major industrial corporations invest heavily in that open source project," Ellison said at a Tokyo news conference. "Every open source product that has become tremendously successful became successful because of huge dollar investments from commercial IT operations like IBM and Intel and Oracle and others," he said.
Yes, financial support from companies has indeed benefited one or another open source project. But to conclude that without this financing the projects would not be successful is completely crazy. On the contrary: many companies only invest in projects that have already become successful without external help. Smaller projects with less visibility have no chance of getting money from large IT companies - these are sometimes supported by companies, but then usually by companies that have directly started this project or market direct products based on it.
But of course, with the successes that a number of open source database systems have, he naturally has to rattle loudly and talk nonsense so that no one notices how pathetic Oracle really is by today's standards.

Why I Don't Like PHP Software
Wordpress is indeed one of the better systems written in PHP. And what happens? There are several sloppy programming practices found within it. Yes, I know, this happens in other languages too. The point is: the Wordpress programmers are relatively well qualified and relatively careful in their work - and yet such problems occur. Among other things, because in PHP the sources lie within the server root, meaning files that are actually only used internally are accessible via HTTP. And because PHP solutions do not inherently perform input validation and proper text quoting. No, sorry, but I simply do not like such a mess.
Disk Inventory X - also provides overviews of where disk space is lost, but with a very clever graphical display.
ID-Design, Inc. | WhatSize - provides a good overview of where disk space is consumed.
Monolingual - removes language versions of OS X that you never use. Brings back a lot of disk space.
Tor GUI Competition
I didn't know about the GUI Competition for Tor - a good tool for securing the privacy of internet users. I've been using Tor for a while now - and at one point I even ran a Tor router - but the use, especially with dynamic network connections, is still a bit clunky for regular end users. Of course, I also hold the opinion that end users should learn more about their computer and therefore the installation and use of Tor should also be feasible for these people - but if we really want Tor to be a sign against state data espionage, then we definitely need graphical interfaces for activation, use, and configuration. Only then will regular users also think about whether they should use it after all.
For this reason, I am also particularly pleased that the competition has now moved into the next phase - the actual programming of the GUIs. And as a stupid Mac mouse pusher, I of course also wish for an OS X interface for this.
By the way, there is a very practical - and in my opinion obvious - application of Tor: public WLAN hotspots. Communication usually takes place unencrypted on them. This makes all accesses directly visible to others - unusable for accessing sites for which you have a password, if these do not also offer SSL immediately. And particularly problematic with all the other unencrypted services with which one likes to play around on the Internet - IRC for example (a private chat is not all that private if you conduct it over a public WLAN hotspot ...). Tor can help here very easily - a local Tor installation on the computer and the client software configured accordingly and you already have a kind of super-VPN.
This is also a reason why I wish for a Tor port to the small Nokia 770 tablet.
I myself do not use Tor for all services - but I generally have a network configuration ready on the Mac, in which Tor and Privoxy are activated by selection (I would like to be able to toggle the socks-forward in Privoxy via a Privoxy-GUI - then I could keep the Privoxy environment generally active and only switch on Tor when needed). This way I can quickly and easily switch on Tor on the go. For Jabber I use Psi, for which I have the Tor service generally activated. For IRC I use XChat-Aqua, which can be easily equipped with various server configurations, so that I can activate or deactivate Tor (many IRC networks do not allow IRC use via Tor).
In my opinion, a GUI on the Mac should integrate into the network environments on the Mac, so that it makes corresponding changes when activated, just as the environment switch does. And you should be able to easily slip new configs under other programs, as was the case with the old Mac Locations, for programs for which the proxy must be entered manually.
Wasabi Systems has a quite useful analysis of what the GPL actually means for companies. Furthermore, there is also a chapter that deals with binary kernel modules - and why these represent a GPL violation.
To the Content Thieves
Once again, as described at Blogbar, there are content thieves around. Here's a preventive explanation of what a CC license with Share-Alike condition and Non-Commercial means: no ads on the pages. No commercial site - for example, paid accounts or similar. And yes, I mean Non-Commercial seriously. Share-Alike also has a simple explanation: a site that reproduces my content must be under the same license as my site.
Those who cannot meet the two conditions (we won't talk about the explanation of Attribution) will have to ask. And this does not mean that a lack of response is a silent consent - those who do not have explicit permission from me and cannot comply with the CC license must keep their hands off my content.
And those who think I can't do anything to them: those who are stupid enough to automatically pull content from RSS feeds should consider that the pulling machine is recognizable (especially for "stationary" services) - and that appropriate feeds can be provided for individual servers if you program your software like I do. And believe me, dear content thieves: the content you would then pull would definitely not please you.
IBM is now gaining momentum
Does anyone remember this ongoing court case between SCO and IBM? GROKLAW brings a series of documents with IBM's demands to various companies. Microsoft, Sun, HP, Baystar - with a lot of very interesting questions. Hey, the procedure could slowly become interesting again.
Net Neutrality at Risk
Deutsche Telekom demands money from content providers - and in doing so, they are echoing the same tune as US telecoms:
Telekom CEO Kai-Uwe Ricke announced that the Telekom plans to charge providers like Google, Yahoo, Amazon, and eBay in the future. It cannot be, he told the "Wirtschaftswoche," that the customer alone pays for the broadband network.
And who guarantees that this will only affect large content providers? And who guarantees that small customers, private sites, etc., will still receive the same service as the big players? Because that's exactly what network neutrality means: that the service is the same for everyone involved. Even if Ricke acts as if he were the customers' advocate, it's really just about the backbone operators wanting to make more money, especially those in the telecommunications sector.
Heise makes it clearer what this demand from the telecoms means: ultimately, the providers will pay multiple times for the same service. First, they pay their host or provider for connectivity. Then they pay again for the same bytes to the backbones. And then the visitor also pays for the same bytes to their provider. This is classic telecoms rip-off (and by that, I mean more than just Deutsche Telekom).
Backbones actually finance themselves through peering agreements with other backbones (where there is asymmetric load distribution) and through their own direct connections to providers and users. Now they want money from parties with whom they do not even have contracts - but only through third-party contracts do they use the services of the telecoms. And that is simply extortion.
Phollowing the Phlopping Phish
Who wants to know more about the embarrassing mishap at Geotrust: Phollow the Phlopping Phish describes the phishing attack from a user's perspective. With screenshots and documentation of how well the site was faked and how little a normal user could see through it.
The Linux Kernel Driver Interface - why the Linux Kernel has not designed its internal kernel interfaces as a "stable binary interface" (or even as a "stable interface").
Browsers are not program starters
Apple Safari automatically executes shell scripts - more precisely, a whole range of techniques come into play. The trigger, however, is the stupid habit of Safari to automatically start the appropriate viewer for certain file types - and sometimes incorrectly assign file types. In general, it is simply a bad idea when a browser tries to classify downloads as safe or unsafe and then passes them on to an external program - because this external program is usually in no way prepared to receive unsafe content. As soon as the browser misjudges, the trojan is functional.
So people: turn off the "execution of safe file types" in Safari. And Apple could take this as an opportunity to finally remove this function from Safari. The few extra clicks won't kill the user ...
Update: and here's the reason why I get a bit pissed off about such bugs - sorry, but this is Microsoft-World, not Unix-World. Please pull yourself together and don't do such nonsense

Know Your Enemy: Learning with VMware - how to build a virtual honeynet with VMware and see what and how is being hacked.
OpenVPN on Maemo - Porting OpenVPN to the Nokia Pad. Could be quite interesting, as you are now a bit too visible to others over free WLAN hotspots.
Firewall providers, sharpen the fillers!
Since Basel II becomes law - and thus it may be that the banks will ask your customers for documentation of IT security before a loan is granted (since IT security is part of the risk assessments in credit scoring):
The operational risks of a company also include the risks arising from the use of information technology in business processes. An active IT risk management is required, which deals with all aspects of IT security for the respective company. Important IT systems must be redundantly available, availability must be ensured, attacks on IT systems from inside and outside must be effectively repelled, contingency plans should be developed, and so on.
And since customers usually do not create their own documentation (which always fascinates me, because actually they should take care of security themselves, so they should also maintain their own documentation), they then demand such documentation from the service provider. Usually one day after they have been asked about the topic (e.g. when the auditor is about to refuse them the seal of approval because the documentation is missing).
Hey, that's a whole new form of corporate extortion: be cooperative, or your next IT security audit for the new loan will go down the drain.
Pressure on Hardware Manufacturers
Suse Linux in the future without proprietary drivers - good thing, in my opinion. The more pressure is put on hardware manufacturers, the more likely we will actually get better OpenSource drivers or interface disclosures.
Mobile? 870 MB are Mobile?
Mobile Offline-Variante der Wikipedia massiv erweitert - it is now 870 MB in size. Somehow, this scares me, as we are already hitting the limit with the 1 GB memory card in mobile devices. Hey, for my Nokia Tablet I only have 512 MB on the memory card! (well, with that I can always search online)
Embarrassing SSL Blunder at GeoTrust
In the USA, there is a case of phishing with valid SSL certificates. There, a certificate was issued via GeoTrust - the guys who also bought Trustcenter in Hamburg after it went bankrupt - to someone who then used it to fake a banking site. And so well that it is no longer easily possible for a customer to determine its authenticity.
SSL is no guarantee - it is only proof that someone has been issued a certificate. But you have to know whether you trust the certificate issuer - and unlike Web-of-Trust approaches, there is usually exactly one single certificate issuer, not a group or even an entire network.
If the vulnerability is in the certification of the certificate issuer, it doesn't matter how many or few bits the key works with ...
Clear, I pack data to Google ...
Privacy advocates are not enthusiastic about Google Desktop Search 3:
On February 9, 2006, a beta version of Google Desktop Search was released, which allows you to find documents stored on different computers. This is achieved by storing the relevant files on the Google server, so you need to have and use a Google account to use this feature.
Great idea. Of course, I'll put data from my workplace on a Google server. Where it's readily available for anyone who gains access to the boxes. Very big idea. Google may have the motto "don't be evil" - but they should also think about the motto "don't be stupid" ...
Powerful Remote X Displays with FreeNX - interesting for remote servers, as it has significantly better responses and lower bandwidth requirements than X or VNC.
VMware Server now free
VMware Server is now free like free beer - and it should remain so after the beta. Great deal, because VMware is after all still the undisputed king among virtualizers - even under Linux. The open-source projects still have a lot to offer to get close to what VMware Server offers.
But if you want to try it out on your own host (which is quite easy due to the simple installation): make sure that the host does not have any other user accounts. Because VMware Server mercilessly uses all accounts that are set up on the system itself. Every user with whom you can log in - and that can indeed be a trivial mail user - can then create virtual machines and control public virtual machines (which are basically all created as root) and delete them.
The whole permission management is generally a bit of a hairy topic with VMware Server - it is decided based on the system permissions for the configuration file of the virtual machine. This is convenient - you just need the known tools - but also quite unintuitive during a first installation. And for example, I couldn't get the permission management for creating machines activated (for this, a special check file is created, whose permissions then say whether a user is allowed to create a new machine or not).
But once it's running smoothly (I had more trouble with X11 on the Mac - ssh -Y instead of ssh -X is the answer), it's a fine thing. Debian guests use minimal memory through the VMware tools, at least when they are not actively in use - and the management with the graphical console or the web interface is also quite nice. I think with a new machine this could really appeal to me - especially since you can then set up such a machine from the beginning with minimal users and push all services into the virtual machines.
However, I have already noticed that my simon is somewhat underpowered when it comes to virtualization. But a Hetzner DS 5000 or 7000 with extra storage could fit quite well there.
.eu Domain Debacle - about the dirty tricks used to infiltrate the Sunrise Period.
HolisTech Limited Free Software, pwsafe - Password-Safe for the Nokia Tablet.
Password Safe - by Bruce Schneier. The Java version 0.5 is compatible with the Maemo version.
pwsafe password database - Command line tool for Password Safe databases.
Holes in the Java Sandbox
Unauthorized file access through Java vulnerabilities - ouch. A sandbox is only as good as its programmers, unfortunately. It must be admitted, however, that the sandbox rarely shows holes. But just because Java is now also spreading further to mobile devices and other devices, such things are naturally becoming more interesting.
AVM could simply write drivers under GPL
AVM warns of restrictions for proprietary kernel modules:
The consequence for AVM would be to stop supporting Linux. A reaction to the email is not yet available. The kernel developers are likely to be little bothered by AVM's threat, as their goal of keeping the kernel and its entire environment free seems to take priority due to their mixed experiences with proprietary drivers. Alternatives to AVM exist, and GPL drivers for AVM hardware are not excluded, even if they do not come from AVM.
Exactly that: Alternatives exist. It's time for the alternatives to pay off with better Linux support - then maybe AVM will also become reasonable. The binary modules without source cause more trouble than joy.
Call me a pessimist ...
... but I feel uncomfortable with such ideas:
Companies should in the future acquire the electronic equivalent of a stamp if they want to be sure that their email reaches the recipients. For fees of up to one cent per message, the mails sent via the service provider Goodmail Systems will be forwarded without spam filtering and confirmed as received.
When will emails from private individuals no longer be delivered unless they go through one of the large providers participating in the payment system? When will citizens' networks or privately operated providers be excluded because they cannot belong to the club of payers?
The possibly upcoming argumentation is simple: only those who pay to a central authority for their website will be enabled for HTTP access in the mandatory proxy of the large providers - because otherwise they are suspected of being a phishing site. And soon, outside of email, some sites would simply no longer exist. It also fits perfectly with the efforts of telcos and cable providers in the USA, who also want to deliver paid content (i.e., content paid for by the telcos) on a priority basis.
Apart from the fact that I definitely trust my own filters more than filters operated for payment by some company on the net. When will there be the first scandal that a spammer has bought access? My statistical spam filter on my server is not corruptible - not perfect, but also not corruptible.
In the establishment of further central filters and control points, I see a real danger to the structure of the Internet - how quickly companies are bought, one could see in recent times. And even if a company like Yahoo today possibly - due to the necessary positioning against Google - is a bit on a cozy course with the user, who guarantees that a media giant does not take over the whole thing? Not everyone is as incompetent as Time Warner ...
Console Password Manager - very interesting tool, stores passwords encrypted with GPG and uses existing GPG keyrings. This way you can also encrypt password files for others (e.g. shared passwords in the company for multiple admins). And it runs on the console.
Book Review -- The Debian System: Concepts and Techniques | Linux Journal - interestingly sounding book about the concepts in Debian.
twill: a simple scripting language for Web browsing - a Python scriptable Web client. Interesting for automated page requests and for specialized robots. Possibly also for testing web applications.
Game Protocols and Firewalls
If someone wants to check out Second Life:
Second Life needs to connect to ports 443/TCP, 12035/UDP, 12036/UDP, and 13000-13050/UDP. You should configure your firewall to allow outbound traffic on those ports, and related inbound traffic.
Ok, so TCP is fine with NAT firewalls - but apparently it also wants all those UDP ports inbound. And why does a game client need 51 UDP ports in a block? And why so many UDP ports at all? Do game designers ever think about what they're doing? In the case of Second Life, apparently not ...
Torvalds: insert foot into mouth
Linus claims to know again - this time about licenses:
The new license requires that all keys necessary to run the software must be delivered with the software, for example in the case of Trusted Computing systems that may require a signature of the programs. In Torvalds' opinion, the regulation also covers the private keys of Linux developers and he is not willing to publish his private key.
Yeah, sure, if I interpret a license in the most absurd way possible, I might come up with such an outlandish idea with enough idiocy. If he now only proves to me that his private key is necessary to make the kernel runnable (because that's what it's about in the corresponding section of the GPL v3), then I would agree with him. However, it's going to be difficult, because so far I have always been able to run all Linux kernels without ever needing any key.
You can be against the switch to GPL v3 - there is definitely a problem with the license change in the kernel with the extremely many contributions and authors - but the above "reason" is simply ridiculous.
Should Windows source be disclosed?
Microsoft gives in to EU in antitrust dispute:
In the antitrust dispute with the EU Commission, the software manufacturer Microsoft has now given in and will disclose the source code of the computer operating system Windows.
Let's wait and see how this disclosure will look. Will every Windows license holder actually be able to view the sources? And will the sources match the system? And which parts of the source will be left out? Will the EU Commission be able to recognize such deceptive packaging?
Microsoft Closes the Gates Against OSS
First, only signed drivers should be accepted:
What Microsoft markets in its documentation as a security gain and as an indispensable feature for Digital Rights Management (DRM) has a bitter aftertaste: So far, only those who equip themselves with corresponding certificates from Verisign and pay around 500 US dollars per year for this can create such a signature.
But from signed drivers (with which open-source drivers will already have a real problem) to signed applications is not far. And for open source projects, it is usually not so easy to get the money for certificates.
When will developers finally discover notebooks?
I mean, when will they finally realize that notebook users are different from desktop users? For example, the environment of a notebook user constantly changes? That the network configuration is not static but dynamic? And that the web proxy is a dynamic setting - it is highly nonsensical to pack these into program configuration files instead of reading them from environment settings? For my part, it can certainly be a place for this in the configs - but then there should also be a way to override this setting from the environment.
Where this has become particularly noticeable to me recently:
- subversion: the proxy configuration is only possible in ~/.subversion/server. Rarely stupid, you can't even refer to an environment variable (at least I can't find anything about it)
- x-chat: the configuration is only done via the GUI. The system-wide proxy in the environment variables should override any local settings in the GUI and be displayed there, there is a reason why the user has set a proxy outside.
This is especially annoying with Unix applications that are ported to OS X Aqua (e.g. X-Chat Aqua is such a case): with real OS X applications, the network settings are used for proxies and the like, so that these applications then use the correct proxy when the network environment is switched. With ported applications, this access to the network settings is missing - but because they are GUI applications, possible settings from the shell startup scripts are not evaluated. Because these are possibly not active at all in GUI applications. Instead, a special property file is read - which is rarely stupid, because it is static and no shell script. Yes, Apple messed that up.
With programs that are started from the shell, you can easily read the proxy settings using scutil and a few lines of Python and put them into the environment - but with GUI applications and even some CLI programs, you fail with the ignorant developers. Bah. Humbug.
Unauthorized access to email is unauthorized
Yes, as an admin, one should be aware of the legal consequences in case of a breach of trust:
According to a decision of the Labor Court Aachen from August 16, 2005, the unauthorized access to other people's emails by a system administrator justifies his immediate dismissal (Az. 7 Ca 5514/04).
Power (in the sense of access to data that is not accessible to others) always means responsibility. By the way, this has been clear to many sysadmins for a long time. It would be nice if politicians (whose power is often much greater) were also aware of this ...
runit - a UNIX init scheme with service supervision - alternative to sysv-init with more possibilities and integrated features like supervise (from the daemontools).
/sandbox/spam-filter - The Trac Project - Trac - Trac branch containing a spam filter that can detect spam in various places through different modules. Unfortunately, previous Trac versions did not have a spam filter.
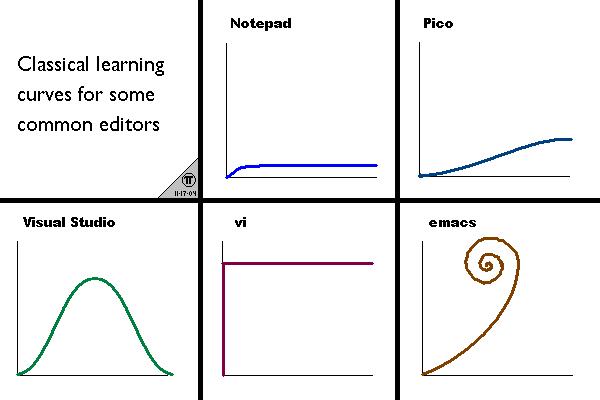
Efficient Editing With vim - Jonathan McPherson - nice reference for more advanced key commands in vi. I don't even use all of them - I should get used to one or the other.